Running the greenbone OpenVAS vulnerability scanner on a Raspberry Pi 4
I’ve been experimenting with the Free / open source vulnerability scanning tool, greenbone, for the last month or so.
So far, I’m really impressed.
Installing greenbone on a Raspberry Pi 4
The official Community Edition documentation is good.
I’m running greenbone on Debian 11 on a Raspberry Pi 4, which is probably far less powerful than the hardware on which it is intended to run. But I am not scanning that many machines - around 20 - and I am happy to do the scans in small batches, so I thought it would be worth a try.
And, so far, so good.
First I tried the docker-based setup, and then I tried (and have stuck with the) source-based setup.
The docker-based setup is much easier, but I found it less stable. And, when it crashed, I could not get it up and running again. I’ll be the first to say that I don’t know much about docker, so I still don’t know what I was doing wrong / what wasn’t working.
The source-based setup is more convoluted, but it “just worked”. And I have found it more stable. I’ve yet to look at keeping greenbone itself up to date though.
Updating the feeds
I’ve seen some complaints that updating the feeds is difficult.
I’m using a cronjob to run a very simple bash script:
#!/bin/bash
sudo -u gvm /usr/local/bin/greenbone-nvt-sync
sudo -u gvm /usr/local/sbin/greenbone-feed-sync --type SCAP
sudo -u gvm /usr/local/sbin/greenbone-feed-sync --type CERT
sudo -u gvm /usr/local/sbin/greenbone-feed-sync --type GVMD_DATA
Perhaps I’ve been lucky but, again, so far, this simple approach has “just worked”.
Running greenbone
I did a few test scans, and I was pleased to see that it picked up some bits I needed to fix. Had it said everything was fine, I’d have been concerned that it was not working properly. Nothing serious, fortunately, but something to do on pretty much every machine.
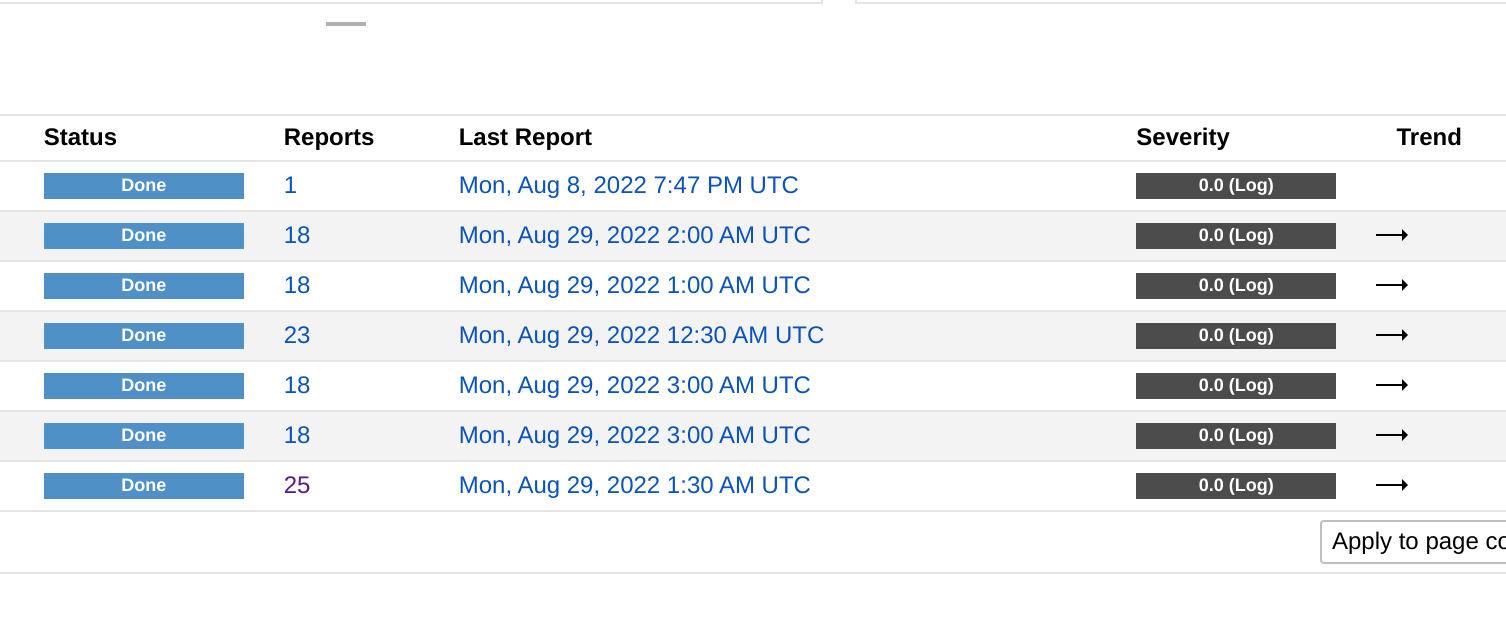
I configured credential-based scanning, so that it can scan the software on the machines rather than just doing network-based scanning. Scanning a target takes about 30 minutes each.
I’ve locked the machine down as much as I can, because I’m using password-protected ssh keys for the authentication.
Once I got the scans running, I set up automated scanning, so that every machine can be scanned automatically each day. I get an email report each time a scan turns up something worth me knowing about, so I can log into the machine in question and check it out.
Initially, I had a bit of a challenge with greenbone and some security software on the targets themselves, as they picked up greenbone as a threat (good!). psad, in particular, resulted in me getting thousands (literally) of email. I used the auto_dl config option for psad to exclude the IP address of the greenbone machine.
I’ve had a few false positives, so I’ve used the “apply overrides” facility to exclude them from the reporting view.
Overall, I’m very impressed. It’s a means of getting yet more useful information about the security of my machines, and I’ve been able to make some definite improvements on the back of it. Plus, since it is ongoing monitoring, as new threats arise (at least, those which make it into the community feeds), I will get notifications, so I can intervene.
You may also like:
- Bypassing captive portal detection on Android 10
- Installing SIP client Blink on Debian 11
- Cloning a Raspberry Pi installation: slow, but working
- Implementing BusKill: shutting down a Debian 11 Bullseye machine when a specific USB device is removed
- Fixing 'tee: command not found' on Debian 11 Bullseye
- Virtualising an existing macOS installation for VirtualBox on Debian 11
- LibreOffice Writer, deleting comments, and tracked changes
- Samsung Galaxy Tab 9.7 and postmarketOS: building a custom image
- Samsung Galaxy Tab 9.7 and postmarketOS: initial impressions
- Microsoft Surface, Debian, and two 4k monitor frustrations
- A year with password manager bitwarden
- Transfer your computers clipboard to a camera-enable mobile device via QR code
- Auto-connecting a VPN on a Wi-Fi connection from a mobile router on Debian 11
- Browsers for people who just want a browser
- Migrating mastodon to Debian 11 Bullseye: fixing the segfault