Brave, Tor, and http-only .onion sites
I set up a .onion hidden service site for our business years ago.
Originally, it was a v2 onion - the older, defunct, but shorter, domains - and now it is a v3 domain, dlegal66uj5u2dvcbrev7vv6fjtwnd4moqu7j6jnd42rmbypv3coigyd.onion.
Catchy.
If you use Tor Browser, and you visit decoded.legal, you should get redirected automatically.
Browsers and sites without https
Normally, if you visit a site without http, in a modern browser, you get a warning:
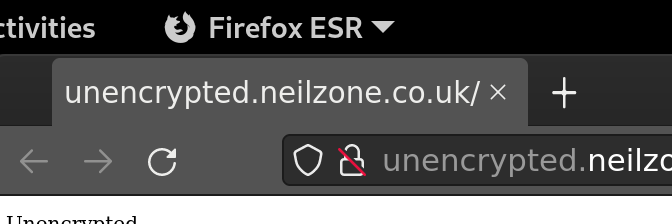
I’m not a huge fan of the padlock, but a warning that the connection is unencrypted is sensible.
.onion and https
With .onion / hidden services, it is slightly different. You can have https on a .onion site, but, because of the encryption within the .onion system itself, it is not essential.
I have not looked into it recently, but getting a TLS certificate for a .onion domain used to be tricky - there were not many vendors willing to offer a certificate for .onion sites - and relatively expensive.
So, for now, our .onion service does not use TLS. It is just http://dlegal66uj5u2dvcbrev7vv6fjtwnd4moqu7j6jnd42rmbypv3coigyd.onion
Update: wow, it has got a lot easier and cheaper! £30ish / year. I’m going to give it a try.
Tor Browser without https
If you visit the site in Tor Browser, it shows that it is a .onion site:
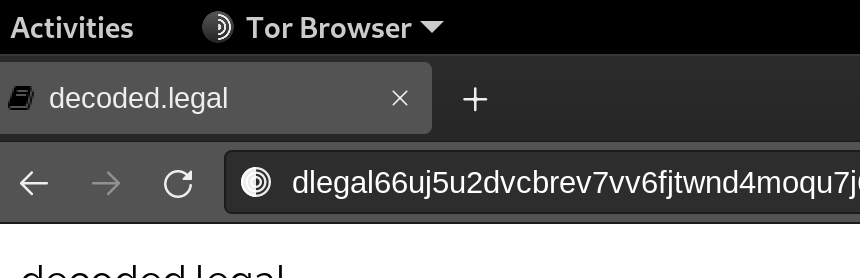
I like this. It is not the same as a site with TLS, or without TLS, and clearly shows it is an onion site.
Brave’s Tor mode without https
If you visit the site in Brave’s Tor mode, it does not show that it is a .onion site. Instead, it shows the normal “insecure” warning:

I can understand why Brave shows this, because that is what it shows for any site which does not use https.
But saying “not secure” feels a bit misleading in the context of a .onion site, which does offer an encrypted connection.
Brave was very responsive when I suggested changes before, so perhaps I should put in a feature request / bug report (not sure which).
Or perhaps I should just get a TLS cert for it.
You may also like:
- Temporarily and automatically changing firewall rules to permit Lets Encrypt certificate renewals
- Browsers for people who just want a browser
- Safer Internet Day 2022. At least we know what were trying to achieve. Right?
- The Wild West Web fallacy
- End to end encryption, and services which let you meet and message people you do not already know
- A prohibition on end to end encryption could leave you with #NoPlaceToHide. And that's not a good thing.
- The end to end encryption debate: 1: the (very) basics of encryption
- Confession time
- Installing Mobian with full disk encryption on PinePhone
- Changing a (known) LUKS passphrase
- Making [vulnerable group] safe online: unpicking those who spin a line to sell their proposal
- Unlocking a LUKS-encrypted partition via ssh on Debian 10 and Debian 11
- DNS-over-https on macOS and iOS
- Supervision is not the same as total surveillance