Auto-unlocking a LUKS volume on an SD card on boot with Debian 11 Bullseye
I am booting Debian 11 on my Surface Pro 6 from a LUKS-encrypted volume.
I have a 256GB microSD card in the slot, and I want that to be encrypted with LUKS too.
For convenience, I want the SD card’s LUKS volume to unlock and mount when the machine boots, rather than me needing to unlock and mount it each time.
I am doing this using a key file, stored on the existing LUKS volume. In other words, I need to unlock the first volume before the SD card will unlock automatically. And that is an acceptable compromise for me. It still means that, if someone steals the microSD card, the data on it are encrypted.
Important!
You need to get the device identifier right for the volume you want to encrypt and unlock throughout this, else you are going to wipe the wrong device.
Use fdisk -l to identify the correct device.
In my care, the SD card was /dev/sda, and it already had a partition of /dev/sda1.
Wipe the SD card and start from scratch
I did:
umount /dev/sda1
wipefs -a /dev/sda1
wipefs -a /dev/sda
I then used fdisk to wipe the device (again?):
fdisk /dev/sda
d, then w.
Then I created a new primarily partition on /dev/sda
fdisk /dev/sda
n, p, 1, accept default, accept default, w.
As I had previously tried to get LUKS working on this, it detected a LUKS signature, and asked if I wanted it removed. I said “Y”.
At this point, I had a refresh SD card on /dev/sda, with a partition on /dev/sda1. But no filesystem on it yet.
Set up LUKS with a passphrase, and add a file system
I used the normal LUKS set-up process:
cryptsetup luksFormat /dev/sda1
Type “YES”, and then enter a passphrase, twice.
When completed, I tested it with luksOpen:
cryptsetup luksOpen /dev/sda1 sdcard
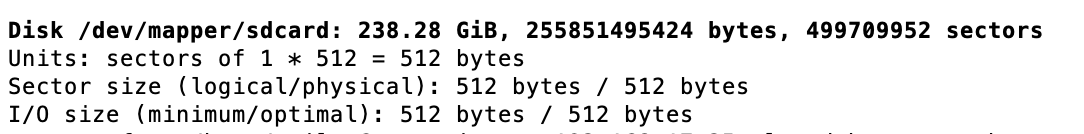
And then used fdisk -l to verify that /dev/mapper/sdcard existed. (It did.)
Now you have a LUKS device available, but no file system. So I formatted it with ext4:
mkfs.ext4 /dev/mapper/sdcard -L encrypted-sdcard
(The -L switch is for the label. This is what appears in Files or your file manager. Even though I have used sdcard throughout, I wanted the visual reminder that it was encrypted, so I used encrypted-sdcard here.)
When done, I closed it:
cryptsetup luksClose sdcard
Outcome: a LUKS volume, which you can unlock with a passphrase, with an ext4 file system.
Configure unlocking with a key file
My goal was to have this SD card unlock automatically as the system booted. (I use LUKS to secure the system itself, so I still need to enter a passphrase to unlock the system to boot it.)
Create a key file:
dd if=/dev/urandom of=/root/keyfile bs=1024 count=4
Lock down permissions:
chmod 0400 /root/keyfile
Check how many LUKS slots are in use:
cryptsetup luksDump /dev/sda1
Add the key file to a LUKS slot:
cryptsetup luksAddKey /dev/sda1 /root/keyfile
(It will ask for your passphrase. I got no feedback other than being returned to the prompt — some guides suggest you get feedback.)
Check again how many LUKS slots are in use — you should now have an extra one:
cryptsetup luksDump /dev/sda1
And, moment of truth, test if you can unlock the LUKS device with the key file:
cryptsetup luksOpen /dev/sda1 sdcard --key-file=/root/keyfile
The sdcard bit is the name you are giving the device for /dev/mapper.
Use fdisk -l to look for a container of the right size mounted on /dev/mapper/sdcard.
If there is one, it has worked!
Outcome: a LUKS volume with a key file added to it, which you’ve tested can unlock the LUKS volume.
Create a mount point
To be able to use this new LUKS device, you’ll need to create a mount point, and then mount it:
mkdir /media/sdcard
mount /dev/mapper/sdcard /media/sdcard
You should now be able to write files to it.
Set up automatic decryption
Once you have verified it is working so far, you’ll need to edit /etc/crypttab to get automatic unlocking, and then edit /etc/fstab so that the unlocked LUKS volume gets mounted for use:
For auto-unlocking, open /etc/crypttab:
vim /etc/crypttab
and add a new line:
sdcard /dev/sda1 /root/keyfile luks
For auto-mounting, open /etc/fstab:
vim /etc/fstab
and add a new line:
/dev/mapper/sdcard /media/sdcard ext4 defaults 0 2
Reboot, cross your fingers, and hope.
With a bit of luck, you will be able to see encrypted-sdcard, or whatever you labelled your volume, in your file manager, or be able to access it at /media/sdcard.
Set user permission
Your normal user account may not be able to write to /media/sdcard, because it is owned by root.
As this is an ext4 filesystem, you cannot add uid= in fstab.
Instead you need to chown it once mounted:
chown neil:neil /mount/sdcard
(If your user account is not neil, change it accordingly.)
There may be a better way of doing this; I’m not sure. But it seems to work for me, and survives reboots.
You may also like:
- Making a Mac Mini power up when power is restored: Debian 11 version
- Installing vanilla Debian 11 on a Raspberry Pi 4
- Unlocking a LUKS-encrypted partition via ssh on Debian 10 and Debian 11
- Installing Debian Bullseye and VirtualBox on a Mac Mini
- Installing Debian 10 Linux on a Microsoft Surface Pro 6
- Raspberry Pi 4 with the PoE+ HAT: LUKS and a working fan
- Fixing a font which shows in macOS Font Book but not in macOS LibreOffice
- Gemini PDA running Debian: a properly portable computer
- Handwriting, and annotating PDFs: a stylus on Debian 10 on Surface Pro 6 compared with an iPad
- Removing the default games in GNOME 3 on Debian 10
- Internet access via iPhone's personal hotspot on Lubuntu 21.04
- Lubuntu 21.04: forcing natural scrolling on a mouse
- Debian 10 on a Samsung NC10
- Running Jitsi on a Raspberry Pi 4
- wireguard via algo: a simpler, faster(ish) alternative to IPSec