DNS-over-https on macOS and iOS
Why bother with DNS-over-https?
I have run a DNS-over-https proxy for a while now, to experiment with it.
First, like the rest of my browsing acting, my DNS traffic is private. But DNS traffic is not, by default, encrypted. DNS-over-https — or “DoH” — fixes that.
Second, encrypting the traffic inhibits interference as well as protecting my privacy. Encryption isn’t just about privacy. Someone sitting in the path between my client and a DNS server could modify the response that I was getting, routing me to the wrong site.
Third, I want to use my DNS server, whatever network I am on. There are a few reasons for this:
- I want to block more than a public network’s DNS is likely to do. I am quite aggressive when it comes to network level filtering, and I’d like it to apply to my traffic, wherever I am / whatever I am connected to. I tend to route all my traffic over a VPN when I’m not connected to a network I trust, but even if I’m not, I’d rather restrict the number of ad servers with which my devices talk, and the number of surveillance / tracker scripts my devices download.
- This is an example of DoH as “safety tech”.
- I may want to access sites or services which are blocked by the DNS specified by the network operator. Different ISPs have different approaches to blocking and filtering. While I do a lot of blocking myself, it’s possible that I want to access a site or service which they have chosen to block. As long as my DNS server is not blocking that resource, DoH means I get — or, at least, increases the likelihood of me getting — access to it.
Firefox has let you specify a DoH server in its Preferences pane for ages, but web browsing in Firefox accounts for only a small fraction of my DNS look-ups. I wanted to route all my DNS look-ups to my server, from my phone and my computers.
I needed a solution (or solutions) which would work for both macOS and iOS. And there is one…
(I don’t know whether tvOS – the operating system of the Apple TV — supports this. That could be interesting if I were travelling more. Update: I’ve successfully installed the .mobileconfig profile on my Apple TV too, but I haven’t tested it yet. It looks like it should work though, which would be interesting if I were travelling abroad and taking an Apple TV with me…)
Warning
This has worked in the handful of scenarios I have tested. What I cannot do is promise that it works in every scenario.
I do not know what Apple does behind the scenes, and whether it definitely means that all your DNS traffic is routed over https.
I also do not know whether a network operator can specify that DoH is not permitted on its network. Firefox has adopted a mechanism to facilitate this users who have had DoH enabled by default, and I do not know whether Apple has done the same. I would hope that there is no equivalent for when someone chooses to enable DoH themselves, but I do not know.
How to route your iOS or macOS DNS look-ups over https
As far as I know, you cannot — yet, at least — configure DoH using either the macOS or iOS GUI.
Instead, you need to use something easy, but still less user-friendly: a simple config file, which you load onto your device as a profile.
It sounds worse than it is.
1.) Create — or just download — a .mobileconfig profile
Pre-made templates for common DoH providers
Someone called Paul Miller has uploaded a lot of template .mobileconfig profiles to Github, and these cover many of the common DoH providers.
If you want to use Google, Cloudfare, or Quad9’s DoH servers, you should be able to download the relevant file and install it on your devices, without needing to do anything else.
Creating a .mobileconfig profile for your own DoH proxy
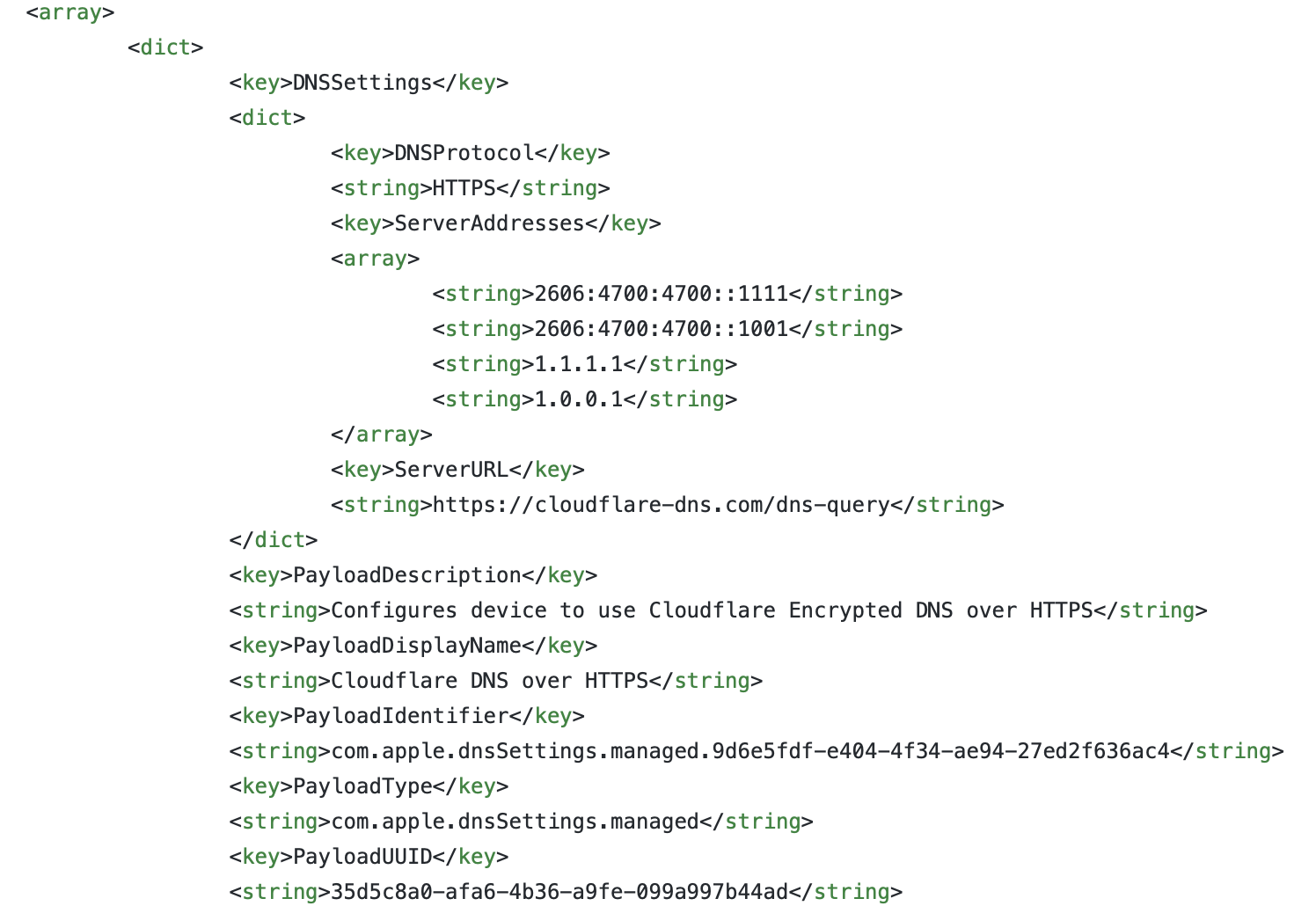
If you run your own DoH proxy and want to use that, download one of the .mobileconfig templates for DoH (e.g. this one, for Quad9), and make a couple of changes:
-
add your proxy’s IP address(es) in the strings in the array under the key
<key>ServerAddresses</key>. -
add the URL of your DoH server to the string under key
<key>ServerURL</key>- e.g.
https://example.com/dns-query
- e.g.
-
change the strings under
<key>PayloadDescription</key>and<key>PayloadDisplayName</key>, so that they reference whatever you call your own system.- You don’t have to do this — it won’t affect the functionality of the profile — but it will make more sense in your device UI if you’ve set these things to text which reflects what you are doing.
2.) Load the .mobileconfig profile onto your devices
If you’re using macOS, just double-click on the .mobileconfig file.
For iOS, you’ll need to get it onto the device. I tend to use AirDrop for this, as it will then prompt you to open it in Profiles, which is what you want.
Once you’ve gone through the profile installation process, you should be routing your DNS look-ups over https to your chosen DoH proxy.
In macOS, it shows up in the Network pane as a new connection.
On iOS, it appears in Settings, alongside VPN connections.
3.) Check it works
Even though it was showing that it was working, I was keen to verify this.
For me, this meant logging into my Pi-Hole instance (since my DoH proxy proxies traffic into Pi-Hole), and checking the access log.
Even though I was connected to a cellular network, and did not have a VPN connection up, I could see my DNS look-ups were going via Pi-Hole. Success!
If you are using a third party DoH service, I’m not sure how you could test it. If you knew there was a domain name you could not resolve over your Internet connection without DoH running, testing using that domain name should work, as long as your ISP is not also doing IP blacklisting / null routing.